
Introduction
In the digital world, accessing online platforms has become a part of everyday life. Whether someone is using email, social media, banking services, or workplace systems, the process usually begins with a Login ID. A login ID acts as a unique identifier that allows a system to recognize a user and provide access to their personal account or profile. It is one of the most basic yet essential elements of online authentication.
A login ID can take many forms, such as a username, email address, customer ID, or employee number. Its primary purpose is to distinguish one user from another within a system. When combined with a password or other verification method, it helps ensure that only authorized individuals can access specific information or services.
As digital platforms continue to grow and more services move online, the importance of login IDs has increased significantly. They not only help manage millions of user accounts but also play a key role in maintaining security, protecting personal data, and organizing digital identities. Understanding how login IDs work and why they are important can help users navigate online systems more effectively and safely.
What Is a Login ID?
A Login ID is a unique identifier that allows a user to access a specific account or system. It is the first piece of information required when signing into most digital platforms. The login ID tells the system which user is attempting to access an account, while the password or other authentication method confirms the user’s identity.
In simple terms, a login ID acts as a digital identity within a system. Every user is assigned or chooses a login ID that is different from others so the system can recognize each account individually. Without this unique identification, platforms would not be able to manage user data, track activity, or provide personalized services.
Login IDs can appear in several different formats depending on the platform or organization. Some systems allow users to create their own usernames, while others automatically generate an identification number. The format often depends on the level of security required and the type of service being provided.
For example, many websites use email addresses as login IDs because they are already unique and easy for users to remember. Corporate organizations often assign employees an employee ID to log into internal systems. Similarly, banks and financial platforms may provide customers with a customer ID or user ID for secure account access.
The main purpose of a login ID is to separate one user from another. In large systems that may contain millions of accounts, this unique identifier ensures that each user’s information, preferences, and activities remain connected only to their own account.
Another important function of a login ID is that it helps systems manage permissions and access levels. In professional environments, different users may have different levels of access depending on their roles. The login ID allows the system to identify the user and provide the appropriate permissions accordingly.
Overall, a login ID serves as the foundation of the login process. It works together with passwords, security codes, or biometric verification to ensure that only authorized users can access specific systems or information. As digital services continue to expand, login IDs remain an essential part of how users interact with technology.
Why Login IDs Are Important
Login IDs play a crucial role in the functioning of modern digital systems. They are not just simple usernames or identification numbers; they serve as the foundation for how platforms recognize users, protect information, and deliver personalized experiences. Without login IDs, managing millions of users on online platforms would be extremely difficult.
One of the most important reasons login IDs are used is user identification. Every online platform needs a way to distinguish one user from another. A login ID acts as a unique label that connects a person to their account, data, and activities. This allows the system to retrieve the correct information whenever the user logs in.
Another major benefit of login IDs is security. Digital platforms store sensitive information such as personal details, messages, financial data, and documents. Login IDs work together with passwords and other authentication methods to make sure only authorized users can access that information. By requiring users to verify their identity before granting access, systems can prevent unauthorized entry.
Login IDs also help in account management. When a user creates an account on a website or application, the system stores various details like preferences, settings, and history. The login ID connects all this information to the correct account so that the platform can deliver a consistent experience each time the user logs in.
Another important role of login IDs is personalization. Many platforms customize content and services based on user behavior. For example, streaming services recommend shows based on viewing history, and online stores suggest products based on previous purchases. The login ID allows the system to track these activities and provide personalized recommendations.
Login IDs also support activity tracking and accountability, especially in professional environments. In workplaces, employees use login IDs to access internal systems, company databases, or communication tools. If changes are made to files or systems, administrators can track which login ID performed the action. This helps maintain accountability and security within organizations.
In addition, login IDs make it easier for organizations to manage large numbers of users. Educational institutions, businesses, and government portals often have thousands or even millions of users. Unique login IDs help keep accounts organized and prevent confusion between users with similar names.
Overall, login IDs are essential for identification, security, organization, and personalization in digital systems. As online services continue to grow, their importance will only increase in ensuring safe and efficient access to digital platforms.
Common Types of Login IDs
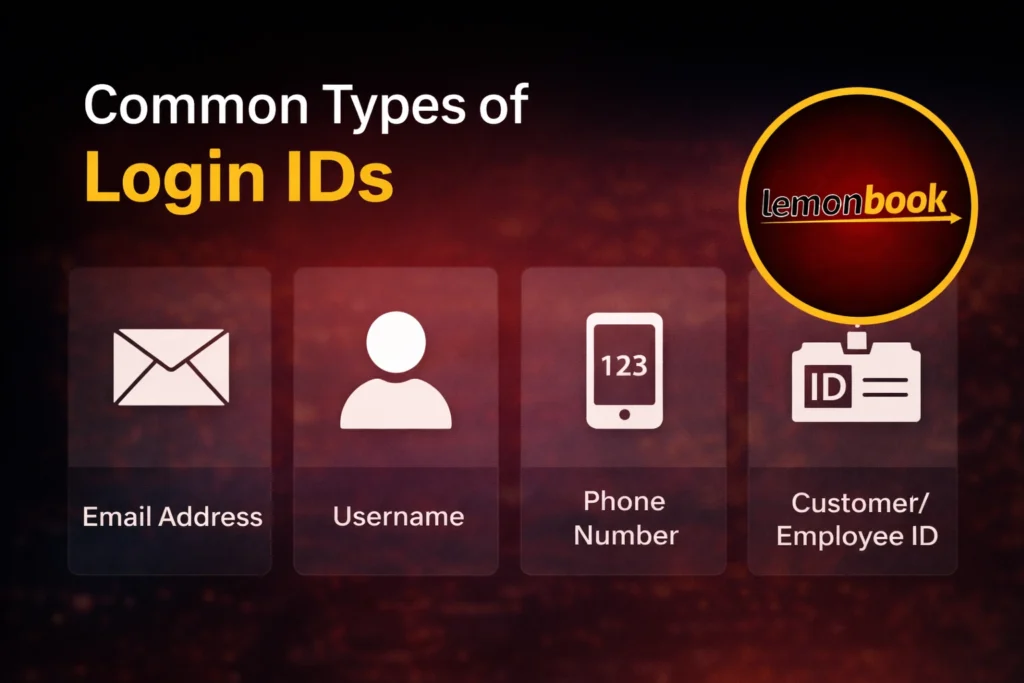
Different platforms and organizations use various formats to identify users when they sign in. The structure often depends on the system’s design, the number of users it manages, and the level of security required. While the concept remains the same, the way these identifiers appear can vary across platforms.
One of the most widely used formats is the email address. Many websites and applications allow people to sign in using their email because it is already unique to each individual. This approach simplifies the registration process and also makes account recovery easier since password reset links can be sent directly to the registered email.
Another common format is the username. Some platforms allow users to create their own usernames during account registration. These names are typically unique within the system and are often used on social platforms, forums, and gaming communities. Usernames also allow individuals to maintain some privacy because they do not necessarily reveal personal information such as an email address.
In certain industries, systems generate a numeric or alphanumeric identification number. For example, banks often assign customers a unique customer ID, while companies may provide employees with a specific employee number to access internal systems. Educational institutions also provide student IDs that allow learners to access academic portals, course materials, and exam results.
Another format sometimes used is the mobile phone number. Many modern applications allow users to sign in using their phone number along with a verification code sent through SMS. This method has become more common with the growth of mobile-first platforms and messaging services.
Some platforms even allow multiple sign-in options. For example, a user might be able to access the same account using an email address, username, or phone number depending on what was used during registration. This flexibility helps improve the user experience and reduces the chances of people forgetting how to access their accounts.
Each of these formats serves the same purpose: identifying a specific user within a system. The choice of format usually depends on convenience, system requirements, and the level of security needed by the platform.
How the Login Process Works
The sign-in process may seem simple from a user’s perspective, but several steps take place behind the scenes to verify identity and allow access to an account. These steps help ensure that the correct person is accessing the correct account while keeping information secure.
The process usually begins when a user visits a website or application and enters their identification details in the sign-in form. This information tells the system which account the user is trying to access. Once the identifier is submitted, the user is asked to enter a password or another verification method.
After the information is entered, the system checks its database to confirm whether the details match an existing account. The system compares the provided password with the stored encrypted password connected to that account. If the information matches correctly, the platform confirms the user’s identity.
Once verification is successful, the system grants access to the account. The user is then able to view their dashboard, access personal data, or use the services provided by the platform. At this point, the system may also load stored settings, preferences, and activity history so the user receives a personalized experience.
If the entered information does not match the stored records, access is denied. Most systems notify the user that the credentials are incorrect and allow them to try again. To prevent unauthorized attempts, many platforms limit the number of sign-in attempts or temporarily lock the account after multiple failed tries.
In more secure systems, an additional verification step may be required. This could include a one-time code sent to a phone, a confirmation email, or verification through an authentication app. These extra layers help strengthen security and reduce the risk of unauthorized access.
Although the entire process usually takes only a few seconds, it plays an essential role in protecting accounts and ensuring that digital services remain secure for users.
Security and Best Practices for Account Access
Protecting online accounts has become increasingly important as more personal and financial activities move to digital platforms. While systems are designed with security measures, users also play a major role in keeping their accounts safe. Following a few best practices can greatly reduce the risk of unauthorized access.
One of the most important steps is creating a strong password. A secure password should include a combination of uppercase letters, lowercase letters, numbers, and special characters. Avoid using easily guessed information such as names, birthdays, or common words. Longer passwords are generally harder for attackers to crack.
Another useful practice is not using the same password across multiple accounts. If the same credentials are used everywhere and one platform becomes compromised, attackers may attempt to access other accounts using the same details. Using different passwords for different services helps limit potential damage.
Enabling two-factor authentication (2FA) is another effective way to strengthen account security. With this method, users must complete a second verification step after entering their credentials. This might include a one-time code sent to a mobile device, an authentication app, or biometric verification such as a fingerprint or facial scan.
Users should also be cautious about phishing attempts. Cybercriminals often send emails or messages that appear to come from trusted companies, asking users to enter their credentials on fake websites. Always verify the website address before entering sensitive information and avoid clicking suspicious links.
Regularly updating passwords is another good habit, especially for accounts that store important data such as banking or business information. Changing passwords periodically helps reduce the chances of long-term unauthorized access.
Using a password manager can also make account management easier. These tools securely store login details and generate strong passwords for different accounts. This allows users to maintain strong security without needing to remember multiple complex passwords.
Finally, users should always log out from shared or public devices after accessing their accounts. Leaving an account open on a public computer can allow others to access personal information.
By following these best practices, users can significantly improve the security of their online accounts and reduce the risks associated with digital access.
Challenges and Issues Related to Login IDs
Although identification systems are essential for accessing digital platforms, they can also create certain challenges for users and organizations. As the number of online services continues to grow, managing multiple accounts and remembering access details can become complicated.
One common problem is forgetting account credentials. Many people use dozens of different online services, and it is easy to forget the username or password associated with a specific platform. When this happens, users often need to go through recovery processes such as email verification or security questions to regain access.
Another issue is duplicate or unavailable usernames. On platforms where users create their own usernames, popular names may already be taken by someone else. This forces new users to modify their preferred name by adding numbers, symbols, or extra characters, which can sometimes make the username harder to remember.
Security threats also present a major challenge. Cybercriminals often attempt to gain unauthorized access to accounts through methods such as brute-force attacks, where automated tools try many possible password combinations. If an attacker already knows the identifier associated with an account, they may attempt to guess the password repeatedly until they find the correct one.
Another growing concern is phishing and social engineering attacks. In these cases, attackers trick users into revealing their credentials by pretending to be trusted companies or services. Fake emails, messages, or websites may ask users to enter their details, allowing attackers to capture the information and misuse it.
Organizations also face challenges in managing large numbers of user accounts. Large companies, universities, and government portals may have thousands or even millions of users. Managing access rights, resetting passwords, and maintaining account security for such a large user base requires advanced systems and constant monitoring.
There is also the issue of account sharing, which can create both security and management problems. When multiple people use the same credentials to access a system, it becomes difficult to track individual actions or maintain proper accountability.
Despite these challenges, most modern platforms continue to improve their security systems and account management tools. Features such as password recovery options, account activity monitoring, and additional verification steps help reduce risks and make it easier for users to manage their accounts safely.
The Future of Login Systems

As technology continues to evolve, the way people access digital platforms is also changing. Traditional systems that rely only on usernames and passwords are gradually being replaced or enhanced with more advanced authentication methods. These new approaches aim to improve both security and user convenience.
One of the most noticeable developments is the shift toward passwordless authentication. Instead of entering a password, users can verify their identity through alternative methods such as one-time login links sent to their email or mobile device. This reduces the risk associated with weak or reused passwords and makes the sign-in process faster.
Another growing trend is the use of biometric authentication. Many smartphones and modern devices now allow users to unlock apps and accounts using fingerprints, facial recognition, or voice identification. Biometric methods provide a higher level of security because physical characteristics are much harder to replicate than traditional passwords.
Technology companies are also working on multi-device authentication systems. In these systems, a user may attempt to sign in on one device while receiving an approval notification on another trusted device. This extra layer of verification helps ensure that only the rightful user can access the account.
Artificial intelligence is also beginning to play a role in improving digital security. Some platforms now use behavior-based authentication, where systems analyze user behavior such as typing patterns, location, and device usage. If the activity appears unusual, the system may request additional verification before allowing access.
Another development is the concept of unified digital identity. Instead of creating separate credentials for every platform, users may eventually be able to access multiple services through a single verified digital identity. Governments and technology companies are already exploring systems that allow individuals to use one secure identity across many platforms.
While usernames and passwords will likely remain in use for many years, the future of digital access will likely focus on making authentication both safer and more convenient. These advancements aim to protect user data while reducing the complexity of managing multiple accounts across the internet.
Conclusion
In the modern digital environment, accessing online platforms has become a routine part of daily life. From social media and email services to banking systems and workplace portals, almost every platform requires users to verify their identity before granting access. The login ID plays a central role in this process by acting as the primary identifier that connects a user to their account.
This unique identifier allows systems to distinguish one user from another, ensuring that personal data, preferences, and account activities remain properly linked to the correct individual. When combined with passwords and additional verification methods, it forms the foundation of secure authentication systems used across the internet.
The importance of login IDs goes beyond simple account access. They help organizations manage large numbers of users, maintain accountability within digital systems, and provide personalized experiences based on user behavior and preferences. At the same time, they are an essential part of protecting sensitive information from unauthorized access.
However, managing multiple accounts and maintaining strong security practices can be challenging for many users. Issues such as forgotten credentials, security threats, and phishing attempts highlight the need for both strong system protections and responsible user behavior.
Looking ahead, the methods used to access digital accounts are expected to continue evolving. Technologies such as biometric verification, passwordless authentication, and unified digital identities are gradually shaping the future of online security. Despite these advancements, the core concept of identifying users within digital systems will remain fundamental.
Understanding how login IDs function and why they matter helps users navigate the online world more safely and effectively. By following good security practices and staying aware of potential risks, individuals can protect their digital identities while enjoying the convenience of modern online services.
Frequently Asked Questions (FAQs)
1. What is a Login ID?
A Login ID is a unique identifier used to access an online account or digital system. It helps the platform recognize which user is trying to sign in. It is usually combined with a password or another authentication method to verify the user’s identity.
2. Is a Login ID the same as a username?
Yes, in many cases a username acts as a Login ID. However, depending on the platform, a Login ID can also be an email address, phone number, customer ID, or employee number.
3. Can two users have the same Login ID?
No, a Login ID must be unique within a system. This ensures that every account belongs to a specific user and prevents confusion between different accounts.
4. What should I do if I forget my Login ID?
Most platforms provide account recovery options. You can usually recover your Login ID by using your registered email address, phone number, or by following the “Forgot Login ID” or “Account Recovery” process on the website.
5. Is a Login ID enough to protect an account?
No, a Login ID alone does not provide security. It must be combined with a password or other authentication methods such as one-time codes, security questions, or biometric verification.
6. Can I change my Login ID?
Some platforms allow users to change their Login ID, while others keep it fixed once the account is created. This depends on the system’s policies and security settings.
7. Why do some websites use email as a Login ID?
Email addresses are commonly used because they are unique and easy for users to remember. They also allow platforms to send password reset links and important account notifications.
8. What is the difference between a Login ID and a password?
A Login ID identifies the user’s account, while a password verifies that the person trying to access the account is the rightful owner.
9. Is it safe to share my Login ID with others?
While the Login ID itself is not always sensitive, sharing it can still increase the risk of unauthorized access attempts. It is always best to keep your account details private.
10. How can I keep my account secure?
You can improve security by using strong passwords, enabling two-factor authentication, avoiding suspicious links, and regularly updating your login credentials.
Our Partner Websites and Trusted Network
In the growing digital ecosystem, collaboration between platforms helps create a stronger and more reliable experience for users. Many online platforms work together through trusted partnerships and networks to provide better services, broader resources, and a more connected environment for visitors. These partnerships allow users to explore additional platforms that offer related services, tools, and information.
One of the platforms connected within this trusted network is lemonbook, which serves as an important partner website. Through this connection, users can access additional resources and explore services that complement the digital experience offered across the network. Partner platforms often work together to maintain quality standards and provide consistent service to their communities.
Another part of this trusted network includes taj777global, a platform recognized within the same ecosystem. Networks like these help expand accessibility for users who are looking for reliable online platforms that operate within similar digital environments.
The network also includes casinoidworld, which is connected through collaborative partnerships. Platforms within the same network often share a focus on user accessibility, digital services, and maintaining a secure online environment for their audiences.
In addition, bettingidindia is another platform that forms part of this broader trusted network. By connecting with multiple platforms, users can explore different services and resources while remaining within a familiar ecosystem of related websites.
Sports and event-based platforms are also part of this network. For example, ipl2026 provides content connected to upcoming cricket events and related digital activities. Such platforms often attract audiences interested in sports updates and event-focused online experiences.
Another platform within this extended network is yoipl2026, which also connects with audiences who follow cricket events and related online platforms. Partnerships between websites with similar audiences help build a wider digital community where users can discover relevant content and services more easily.
Trusted networks like these play an important role in the online world. They help users discover new platforms, expand access to related services, and create a more connected digital ecosystem. By collaborating with partner websites, platforms can continue to grow their reach while maintaining strong relationships within the broader online community.